This is our core technology business, where out technical expertise meet your real-life information security problem. We aim to provide range of services that will give you deep understanding over your network infrastructure, network traffic, overall security posture.
We believe in technological aspect, security can be achieve with the right tools, right configuration, and complete visibility at various level in your network environment.
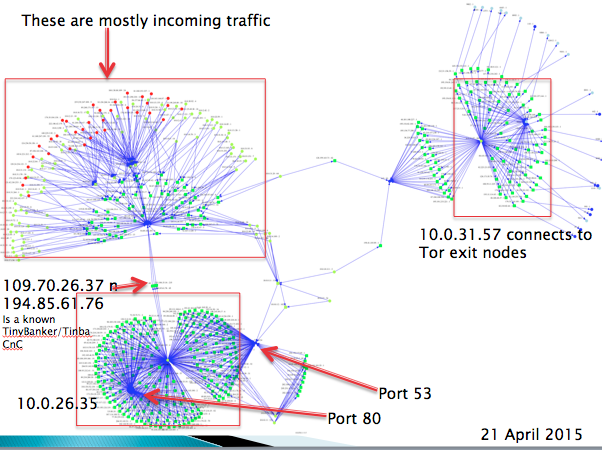
NETWORK FORENSIC
Our network forensic service will provide a deep understanding of what is happening in your network. We will placed our network capture device in your network in inline mode, or port mirroring. Customer will have options to collect the full packet capture, or only the packet header. This might be critical in some network environment where data confidentiality is critical.
NETWORK MONITORING
Our network monitoring will provide a higher level view of your network, revealing a few aspects that would be the key in solving your network problem.
- Capacity planning
- Detecting abusive application and user
- Network application profiling
- Potential compromised machine in your network
- Any potential network device misconfiguration